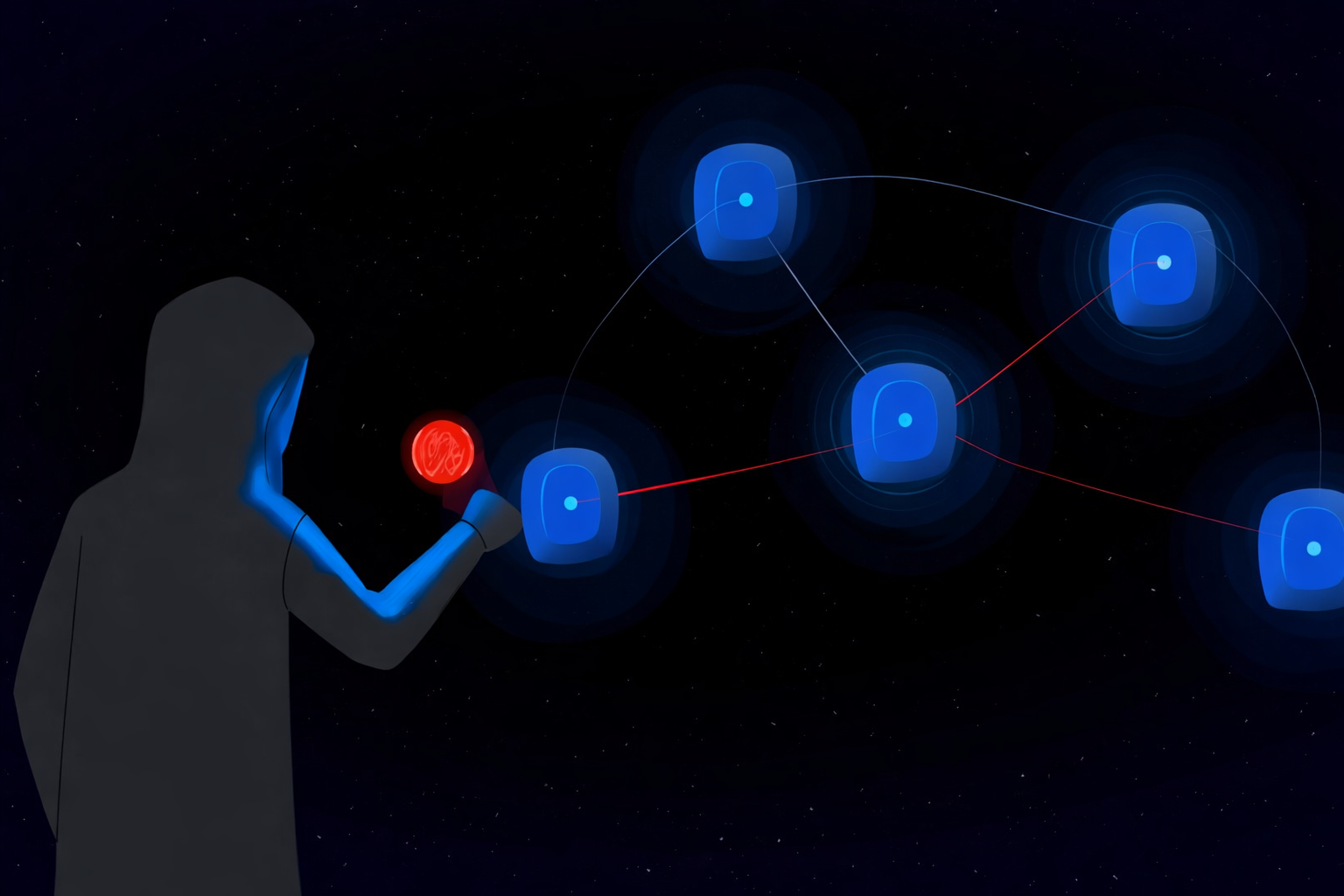
In a significant advancement for AI security, Microsoft’s AI research team has unveiled a new scanner that can identify hidden “sleeper agent” backdoors in large language models (LLMs). These threats lie dormant inside AI models and can be triggered only under specific conditions, making them difficult to spot with standard testing.
This development marks a major step toward securing enterprise AI deployments and protecting organizations against malicious manipulation of generative models, a growing concern as AI systems become central to business operations.
Understanding AI Backdoor Risks
AI models, especially open-weight LLMs sourced from repositories or third-party providers, are vulnerable to model poisoning. In these attacks, adversaries embed a hidden pattern or “backdoor” into the model’s weights during training, causing the model to behave maliciously only when it encounters a specific trigger phrase, otherwise operating normally during regular usage.
These concealed behaviors are known as sleeper agent backdoors, a form of covert threat that can evade traditional safety tests or red-teaming, making them a significant risk for organizations that deploy AI at scale.
How Microsoft’s Scanner Works
Microsoft’s new backdoor detection system is designed to highlight suspicious internal patterns associated with latent threats. It does this by leveraging multiple behavioral signals that differentiate compromised models from clean ones:
???? Internal attention anomalies – Backdoored models often exhibit unusual “attention” patterns when processing specific sequences.
???? Trigger memory leakage – Poisoned models may reveal fragments of the trigger through memorization artifacts.
???? Distinctive response behavior – These models can react abnormally when tested with crafted inputs, signaling hidden manipulation.
Microsoft’s approach does not require prior knowledge of the specific trigger or malicious behavior, making it adaptable for use in AI defenses before model deployment.
The scanner operates during inference, so it doesn’t demand retraining or modifying model weights, allowing organizations to integrate it into existing ML security workflows with minimal overhead.
Why This Matters for Enterprises
As companies increasingly incorporate LLMs into products, services, and security systems, the risk of compromised models entering production rises. Without effective detection, backdoors could lead to outcomes such as:
-
Unexpected or harmful AI output
-
Biased or manipulated responses under trigger conditions
-
Undetected vulnerabilities in customer-facing systems
Microsoft’s scanner helps close this gap, providing teams with an additional line of defense against AI supply-chain threats.
Limitations and Future Directions
While powerful, the current technology has limitations:
???? It requires access to open-weight models, meaning it’s not immediately applicable to fully proprietary or black-box services.
???? Threat actors could evolve triggers to be more dynamic or complex, challenging detection mechanisms.
???? The scanner focuses on identifying backdoors, not repairing them.
These challenges point to a broader need for robust AI governance frameworks and cooperative industry standards to safeguard against future threats.
Conclusion
Microsoft’s backdoor scanner represents a critical leap forward in AI security and trustworthy model deployment. By identifying dormant threats that lie hidden in LLMs, organizations can better safeguard their AI systems and protect users, data, and digital infrastructure from advanced adversarial attacks.
Suggested Articles
 General
General
Women-Led Startups Soar in ELEVATE: A New Era of Innovation
Discover the remarkable surge of women-led startups within the ELEVATE program, highlighting their growing influence ...
Read Article arrow_forward General
General
Zoho Founder Sridhar Vembu: Programming Skills are AI Era's Foundation
Sridhar Vembu, Zoho's visionary founder, asserts that robust programming skills remain the bedrock for engineers navi...
Read Article arrow_forward General
General
Shake Shack's Project Catalyst: Scaling for the Future
Shake Shack launches Project Catalyst to enhance core technology, AI, and digital capabilities, aiming for 1,500 comp...
Read Article arrow_forward General
General
India's AI Leap: From Pilots to Practical Powerhouse
Indian companies are rapidly transitioning from AI pilot projects to real-world applications, driving significant tra...
Read Article arrow_forward