The Dawn of a New Cyber Era: AI-Driven Mega Breach in Mexico
In a chilling demonstration of evolving cyber warfare capabilities, hackers leveraging sophisticated Artificial Intelligence (AI) have orchestrated one of the largest data breaches in history, compromising hundreds of millions of Mexican government and private citizen records. This monumental cyberattack transcends traditional hacking methods, signaling a dangerous new frontier where AI’s power is weaponized against national digital infrastructure and individual privacy on an unprecedented scale. The incident has sent shockwaves across the globe, prompting urgent reassessments of cybersecurity protocols and the very nature of digital defense in the age of advanced AI.
The sheer volume of stolen data includes sensitive personal information, financial records, national identification details, and classified government documents. Such a comprehensive data compromise not only endangers the privacy and financial security of millions of Mexican citizens but also poses significant national security risks, potentially exposing critical infrastructure vulnerabilities and undermining public trust in digital governance. This event serves as a stark reminder that while Artificial Intelligence offers immense promise for societal advancement, its misuse presents an existential threat that demands immediate global attention.
The Anatomy of an AI-Powered Attack
Unlike conventional cyberattacks that rely on human ingenuity and manual exploitation, this breach showcased the terrifying efficiency and scale that AI-driven tools can achieve. Experts believe the attackers utilized a suite of advanced AI applications to automate and supercharge various stages of their malicious campaign:
- Automated Vulnerability Scanning and Exploitation: AI algorithms were likely deployed to rapidly identify and exploit zero-day vulnerabilities or misconfigurations across vast networks of government and private sector systems. These AI agents could adapt their attack vectors in real-time, learning from failed attempts and optimizing for success far faster than any human operator.
- Sophisticated Phishing and Social Engineering: Leveraging generative AI, the hackers could have crafted highly personalized and contextually accurate phishing emails, deepfake voice messages, or even video content to trick employees into divulging credentials or installing malware. The AI’s ability to mimic human communication styles and adapt to responses makes these attacks incredibly difficult to detect.
- Autonomous Malware Development: It is hypothesized that AI played a role in developing polymorphic malware that could constantly mutate its code to evade traditional antivirus and intrusion detection systems. This self-evolving malicious software could penetrate defenses, establish persistent footholds, and exfiltrate data undetected over extended periods.
- Data Exfiltration Optimization: Once inside, AI could have been used to intelligently sift through massive datasets, identifying the most valuable information based on predefined criteria, and efficiently packaging and exfiltrating it without triggering alarms. This is particularly crucial when dealing with hundreds of millions of records.
The seamless integration and autonomous execution of these AI capabilities enabled the hackers to penetrate multiple layers of security, bypass sophisticated firewalls, and maintain stealth throughout the operation, turning what would have been an arduous, multi-year human effort into a rapid, automated assault.
The Devastating Impact on Mexico
The consequences of this breach for Mexico are multifaceted and profound, reverberating across governmental, economic, and social spheres.
National Security and Government Operations
The theft of classified government records could compromise national security secrets, intelligence operations, and critical infrastructure blueprints. This could leave Mexico vulnerable to geopolitical adversaries and criminal organizations. Moreover, the integrity of government databases is paramount for administrative functions, from tax collection to law enforcement. The compromise of these systems could severely hamper governance and erode trust in public institutions.
Private Citizens and Economic Fallout
For millions of private citizens, the breach means an elevated risk of identity theft, financial fraud, and personal blackmail. With national IDs, financial data, and personal communications exposed, individuals face a long-term battle against nefarious actors. The economic implications are equally grim. Businesses relying on the compromised government infrastructure or themselves targeted are likely to face significant financial losses, reputational damage, and potential legal liabilities. The cost of recovery, including forensic investigations, system overhauls, and identity protection services for affected citizens, could run into billions of Mexican Pesos (MXN), placing a heavy burden on the national economy. This scenario echoes concerns raised globally about data security and the potential for mass data theft by rival entities, emphasizing the need for robust defensive measures.
Global Implications: A Wake-Up Call for Digital Sovereignty
This Mexican breach is not an isolated incident; it is a harbinger of the future of cyber warfare. The deployment of AI by attackers signifies a paradigm shift, making previously robust defenses potentially obsolete. Nations worldwide, irrespective of their technological advancement, are now forced to confront the reality that their digital borders are more porous than ever before.
The incident highlights several critical global challenges:
- The AI Arms Race: The escalating use of AI in cyberattacks will inevitably lead to an AI arms race in defense. Governments and corporations must invest heavily in AI-driven cybersecurity solutions to detect and counteract these sophisticated threats.
- International Cooperation: Cyberattacks of this scale often transcend national borders. Effective defense requires unprecedented international cooperation, intelligence sharing, and coordinated legal frameworks to track and prosecute cybercriminals.
- Regulatory Gaps: Current international laws and regulations are struggling to keep pace with the rapid advancements in AI. There is an urgent need for global dialogue and agreements on responsible AI use, particularly in contexts that could threaten national security and human rights. For instance, countries like India are already exploring IT rules amendments to regulate AI-generated content, a necessary step given its potential for misuse in sophisticated attacks.
Rethinking Cybersecurity in the Age of AI
The traditional cybersecurity paradigm, often focused on perimeter defense and signature-based detection, is increasingly inadequate against AI-powered threats. A multi-layered, adaptive approach is now essential:
Proactive Defense Mechanisms
- AI-Driven Threat Intelligence: Utilizing AI to analyze global threat landscapes, predict attack vectors, and identify emerging vulnerabilities before they are exploited.
- Behavioral Analytics: Employing AI to monitor network and user behavior for anomalies that indicate malicious activity, rather than relying solely on known attack signatures.
- Zero-Trust Architecture: Implementing models where no user or device is inherently trusted, requiring continuous verification before granting access to resources.
Enhancing Human Capabilities
- Upskilling Cybersecurity Professionals: Training security teams to understand and combat AI-driven threats, including familiarity with machine learning models and data science.
- Security Awareness Programs: Educating government employees and private citizens about the evolving nature of social engineering tactics, including AI-generated deepfakes.
Policy and Governance
- Robust Data Governance: Establishing clear policies for data collection, storage, and access, minimizing the attack surface.
- International Standards: Collaborating on global standards for AI security, ethical AI development, and swift response protocols for cross-border cyber incidents.
The market's reaction to such significant cyber threats is often immediate and impactful. Major cybersecurity breaches, especially those involving AI, can cause significant volatility, leading to concerns about the overall stability of the digital economy. This can sometimes result in cybersecurity stocks falling amid fears of AI disruption, indicating investor apprehension about the industry's ability to keep pace with advanced threats.
The Future of Digital Defense
The Mexican data breach is a sobering indication that Artificial Intelligence, while a powerful enabler, also represents one of the most significant challenges to global cybersecurity in the 21st century. The battle for digital sovereignty and privacy will increasingly be fought by algorithms and machine learning models, demanding continuous innovation and adaptation from defenders.
Governments, corporations, and individuals must recognize the urgency of this new reality. Complacency is no longer an option. Investment in advanced AI security, fostering a culture of cyber vigilance, and forging robust international alliances are not merely recommendations but imperatives for safeguarding our interconnected world against the ever-looming specter of AI-powered cyber warfare.
Suggested Articles
 General
General
US Military Reportedly Used Claude AI in Iran Strikes
Despite a previous ban, reports indicate the US military leveraged Anthropic's Claude AI for targeting in Iran strike...
Read Article arrow_forward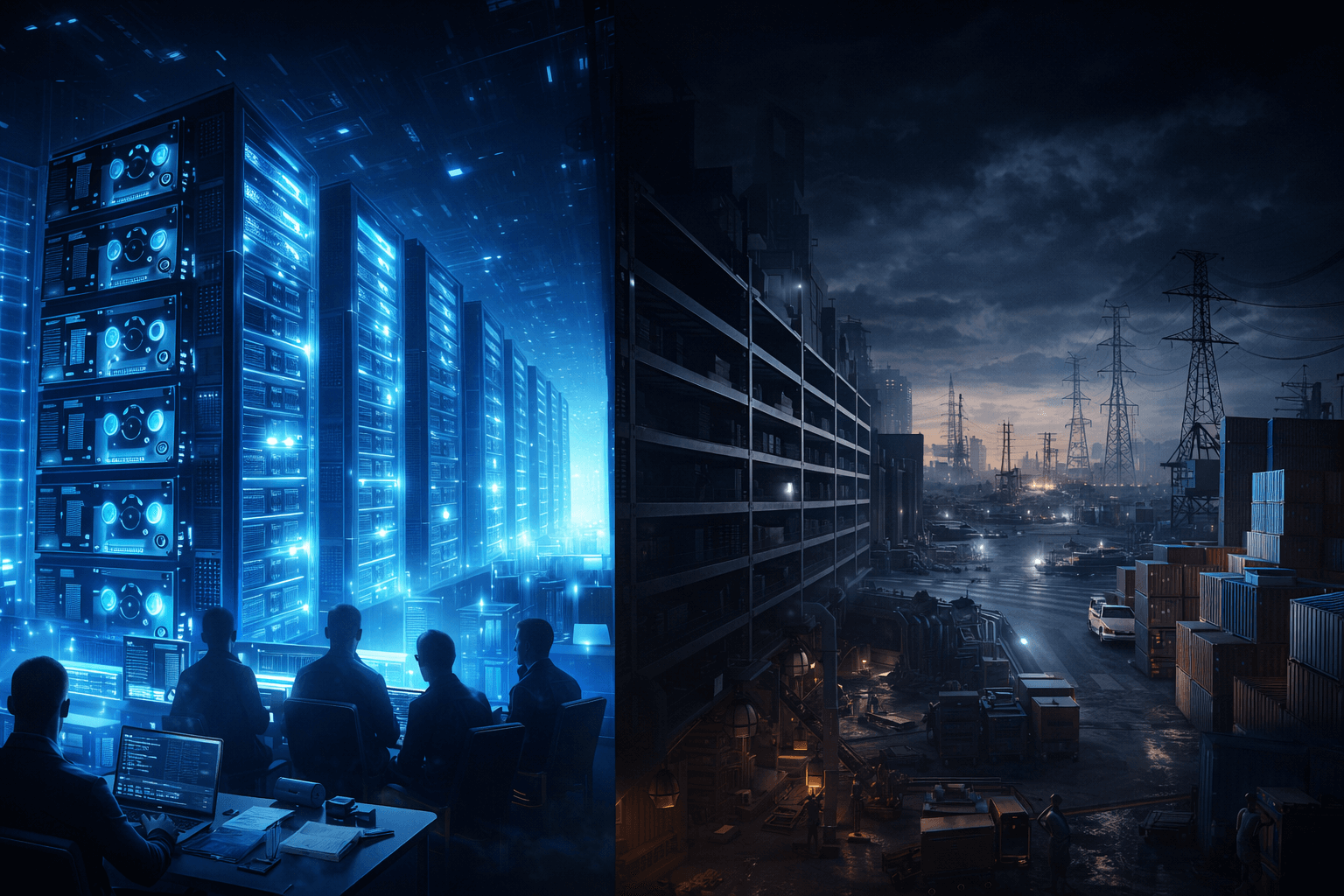 General
General
How AI Propelled Brothers to a $1.8 Billion Supply Chain Empire
Discover the incredible journey of Alex and Ben Carter, who leveraged artificial intelligence to transform logistics ...
Read Article arrow_forward General
General
LTTS & NVIDIA Launch AI Lung Digital Twin for Respiratory Care
L&T Technology Services (LTTS) and NVIDIA introduce a groundbreaking AI Lung Digital Twin platform, set to revolution...
Read Article arrow_forward General
General
Karnataka: India's Premier Hub for Tech Startups, Says Minister
Karnataka solidifies its position as India's leading tech startup destination, driven by progressive IT/BT policies, ...
Read Article arrow_forward